Service
Audit & Traceability Systems
Traditional logs are not enough when access decisions, sensitive actions or administrative changes need to be verified later. Audit systems record actions as structured, verifiable data so the business can reconstruct what happened when it matters.
Operational fit
Where This Service Is The Right Fit
Use this to judge whether the problem is mainly structure, control, and workflow enforcement rather than feature volume.
This Is A Fit If
- Systems handling sensitive operations or data.
- Businesses requiring accountability and traceability.
- Platforms where auditability is critical.
Typical Failures
- Unreliable or incomplete logs.
- Inability to investigate incidents properly.
- Lack of accountability for actions.
- Compliance and audit challenges.
Deliverables
What You Get
The service is structured around operational reliability, not feature volume.
Benefits
- Full traceability of actions and decisions.
- Reliable investigation capability.
- Stronger accountability and control.
- Increased trust in system data.
Deliverables
- A system with structured, verifiable audit trails.
Delivery Process
How The Work Moves
The work is staged so the system logic, scope, and delivery checkpoints stay readable as the build progresses.
Step 01
Define what events must be recorded and why.
Step 02
Design audit structures and integrity mechanisms.
Step 03
Implement event recording and traceability logic.
Step 04
Validate audit flows under real scenarios.
Start The Conversation
Start With The Product You Need To Build
Describe how the operation works, what has to stay aligned, and what the system needs to handle. That is enough to start the conversation.
Related Example
A System In The Same Operating Range
Related example
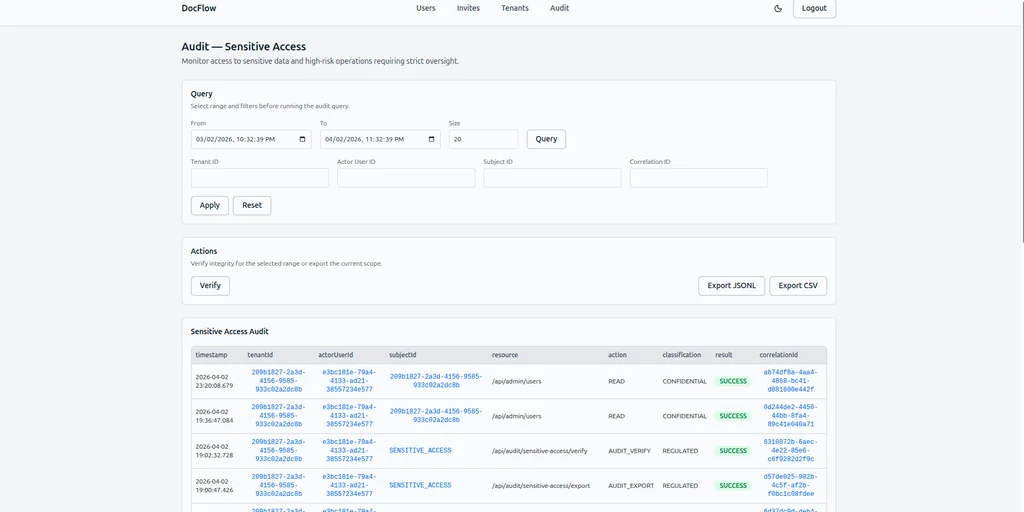
DocFlow: Identity-Bound Access & Verifiable Audit System
For multi-tenant platforms where identity, membership and access must remain consistent under administrative changes, this system enforces identity binding, tenant membership and role-based access while recording every security-relevant action as verifiable audit data. It is designed for systems where access, accountability and auditability cannot rely on logs or manual processes.
Do you need to prove what happened inside your system?
Related Pattern
Access drift
If access depends on email threads, role notes, or trust in ordinary logs, the system is not the thing enforcing who can do what.
FAQ
Frequently Asked Questions
The questions below cover fit, scope boundaries, and what this service is meant to control operationally.
How is this different from standard logging?
Logs are informal and can be incomplete or altered. Audit systems record structured, verifiable events designed for traceability and investigation.
Can audit data be trusted in critical situations?
Yes. Systems can be designed with integrity mechanisms to ensure events are consistent, traceable and resistant to tampering.
What kind of actions can be tracked?
Access changes, data modifications, approvals, administrative actions and any event that requires accountability.
Who typically needs this level of traceability?
Systems handling sensitive data, financial operations, multi-tenant platforms or any environment where accountability and investigation matter.
Is this overkill for a normal application?
For simple systems, yes. For systems where actions must be provable and traceable, it becomes a critical capability, not an optional feature.